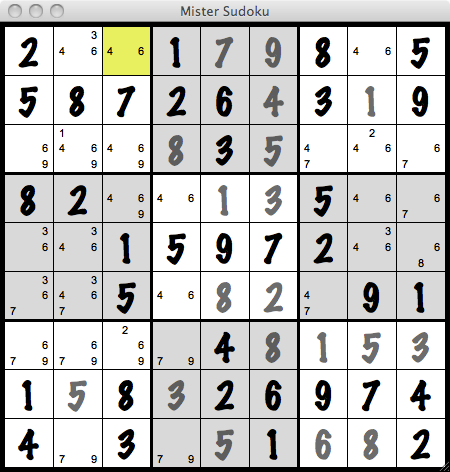
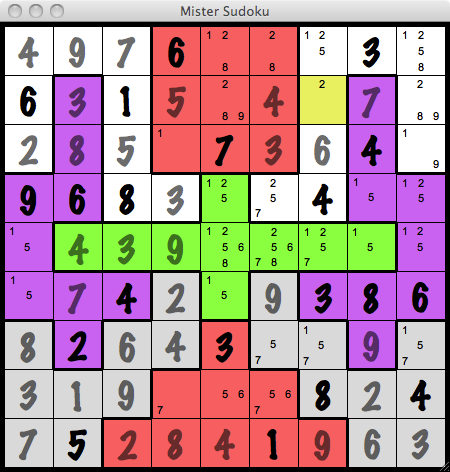
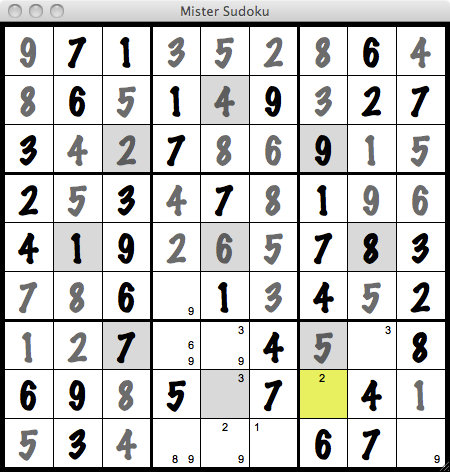
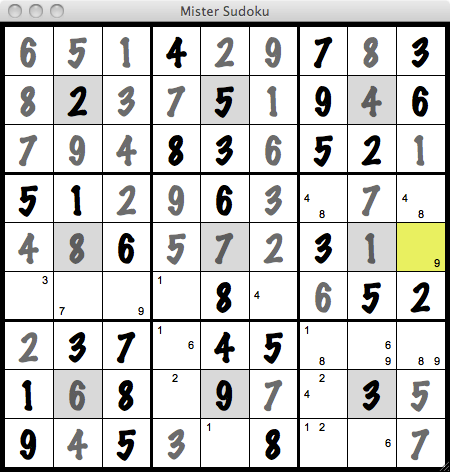
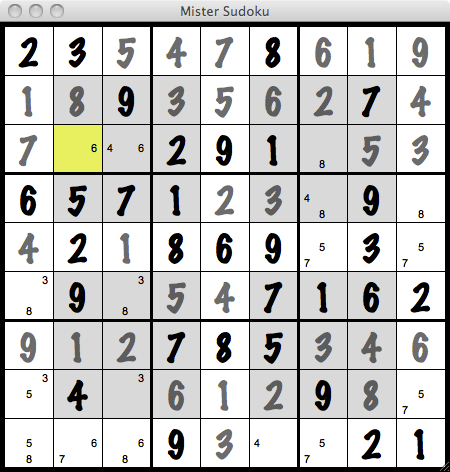
In a Sudoku puzzle, if two cells in the same row have exactly the same two digits as possibilities, then such two digits must be in either one of these two cells and cannot be candidates in any other cells of that row. The same reasoning can be used for any columns and any 3x3 boxes. The technique is called naked pair.
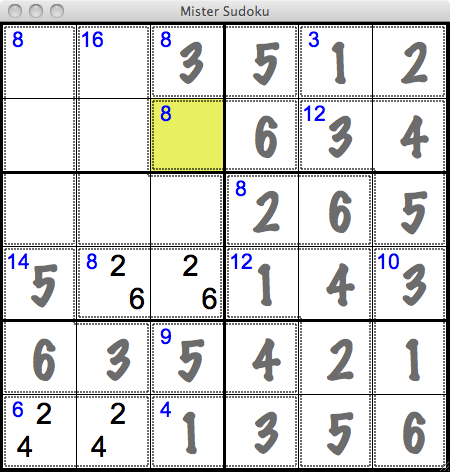
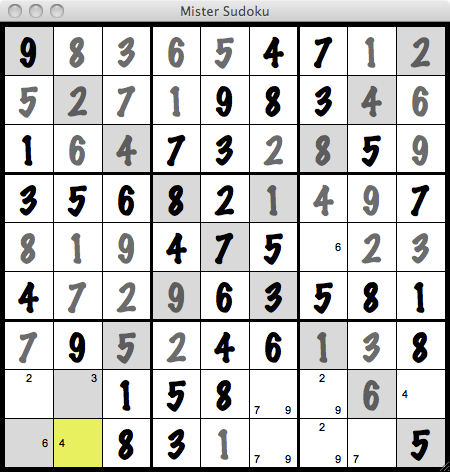
This technique can be applied to more than two digits. It is called naked triplet if three digits are involved and naked quad if four. The number of cells must be the same as the number of digits. But each of the digits involved need not be a candidate of all cells. In other words, each cell has a subset of the digits involved as candidates for that cell.